Enumerating Common Ports: A Pentester's Field Guide
Port enumeration is where engagements are won or lost. Here's how I think about it — what each port tells you, what to probe first, and where the bodies are buried.
Why it mattersBefore you can exploit anything, you need to understand the attack surface. Every open port is a door. Some are deadbolted. Some are wide open. And some have a faulty lock that looks secure until you lean on it. Port enumeration is how you figure out which is which.
A lot of people just run a default Nmap scan, glance at the output, and move on. That's a mistake. The version strings, the service banners, the unexpected ports on non-standard numbers — that's where the interesting stuff lives. Slow down and read what the target is telling you.
The scan itselfI typically run a staged approach: fast TCP sweep first to get the lay of the land, then a deeper service version scan on open ports, then targeted UDP against the ports that matter.
---------------------------------------------------------------------------------------
nmap -p- --min-rate 5000 -T4 <target> -oN ports.txt
nmap -p <open_ports> -sV -sC -O <target> -oN services.txt
nmap -sU -p 53,67,69,111,123,161,500 <target>
---------------------------------------------------------------------------------------
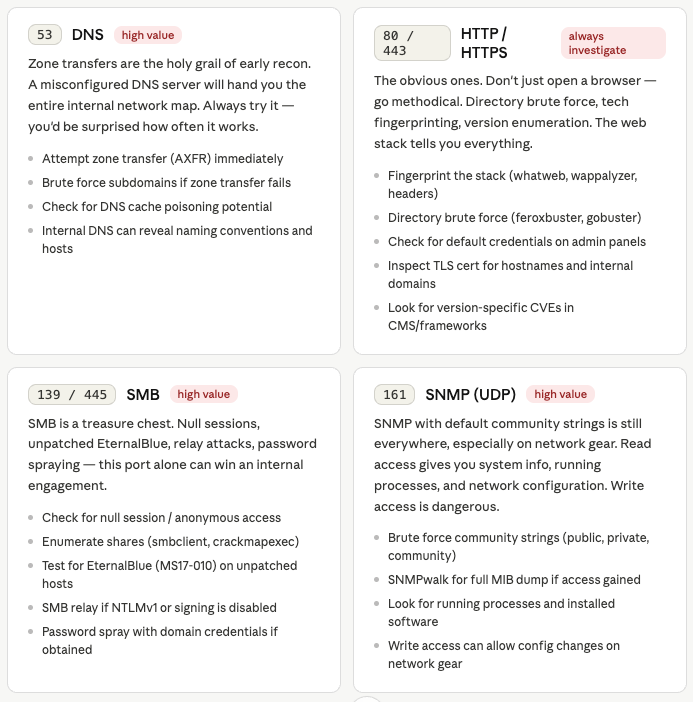
Don't skip UDP. SNMP on 161, DNS on 53, TFTP on 69 — these are routinely misconfigured and routinely ignored by pentesters who never bother with the slower scan.
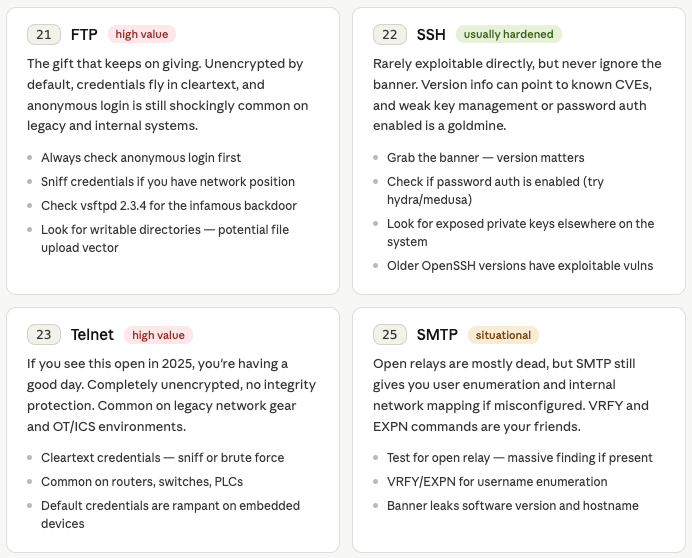
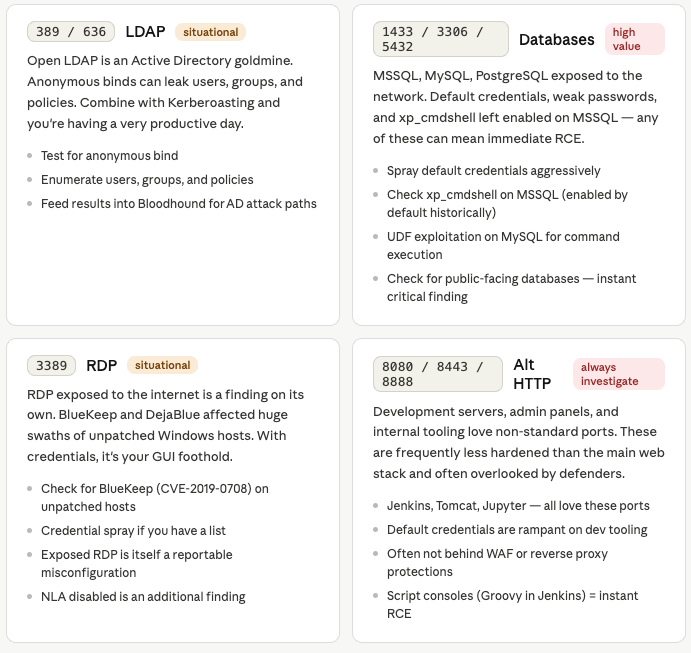
Common ports — what they mean offensively
The mindset
"Every open port is a conversation the host is willing to have. Your job is to figure out what it's willing to say — and then ask the questions it wasn't expecting."
The biggest mistake I see is treating port enumeration as a checkbox rather than a thinking exercise. Yes, run your Nmap. Yes, use your scripts. But then sit with the output. Why is port 8080 open on a domain controller? Why is SNMP exposed on a workstation? Why does the SSH banner say a version from 2014?
The anomalies are where the findings live. The boring expected ports are table stakes. What you're really looking for are the ports that shouldn't be there, the services that are older than they should be, and the configurations that made sense to someone three sysadmins ago and have never been reviewed since.
Enumerate thoroughly. Think offensively. And never skip UDP.
Signed_Ro0t